Can Cybersecurity Work From Home? If you’ve ever wondered whether it’s possible to keep our digital world safe while working remotely, you’re not alone. With the rise of remote work, many companies are grappling with this very question.
In this article, we’ll explore the exciting world of cybersecurity and delve into whether it can effectively function from the comfort of home. So, grab a snack and get ready to dive into the fascinating realm of virtual security!
As technology continues to advance, so do the methods of cybercriminals. They constantly find new ways to exploit vulnerabilities and gain unauthorized access to our data. In response, cybersecurity professionals work tirelessly to protect our digital assets from these threats. But can they do it from home? That’s what we’re here to find out. Get ready for an adventure through firewalls, encryption, and virtual private networks!
Let’s unleash our inner tech wizards and discover if cybersecurity can indeed work from home!
Can Cybersecurity Work From Home?
Discover the possibilities of cybersecurity working from home! With the advancements in technology, remote work is now feasible for cybersecurity professionals. Boost your productivity and flexibility while ensuring network security.
Stay connected with team members and clients through secure communication channels. Implement appropriate security measures, such as VPNs and secure remote access, to maintain the confidentiality of sensitive information. Embrace the new era of work without compromising on cybersecurity.
Rise of Remote Work and Its Impact on Cybersecurity
The emergence of remote work has brought about numerous benefits, such as increased flexibility and improved work-life balance. However, it has also presented new cybersecurity challenges. When employees work outside the traditional office environment, they may use personal devices, access public Wi-Fi networks, or connect to unsecured networks, making them more vulnerable to cyber-attacks.
Additionally, remote workers may lack the robust security infrastructure utilized in traditional office settings. This creates potential entry points for hackers and cybercriminals to exploit and gain unauthorized access to sensitive company data. Therefore, organizations must adapt their cybersecurity practices to mitigate these risks and protect both their employees and confidential information.
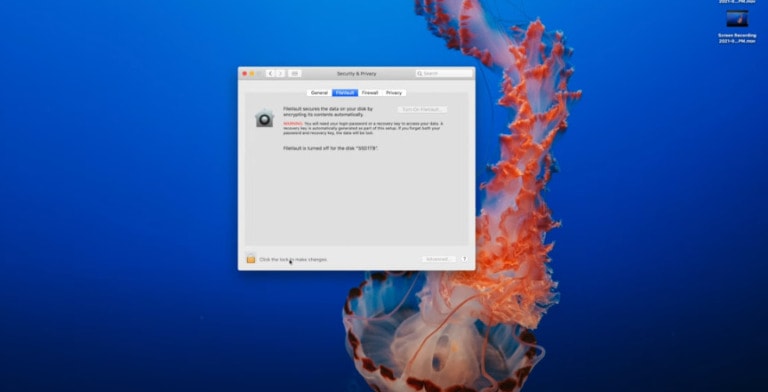
Implementing strong authentication measures, encrypting sensitive data, and providing employees with secure virtual private network (VPN) connections are some of the strategies organizations can employ to bolster cybersecurity in a remote work setup.
Role of Employee Education in Remote Cybersecurity
One of the crucial components of a strong cybersecurity strategy in a work-from-home setting is employee education. Properly training and educating employees about cybersecurity threats and best practices can significantly minimize the risk of security breaches.
Employees should be well-versed in identifying suspicious emails, recognizing phishing attempts, and understanding the importance of strong passwords. By creating a culture of security awareness and continuous education, organizations can empower their employees to become the first line of defense against cyber threats.
Moreover, organizations need to establish clear policies and guidelines regarding the use of personal devices, accessing company networks, and sharing information. Regular training sessions and workshops can ensure that employees are up to date with the latest cybersecurity practices and help foster a security-minded workforce.
Evolving Landscape of Cybersecurity Technologies
As the remote work trend continues to grow, cybersecurity technologies are evolving to meet the challenges posed by this new paradigm. From advanced antivirus software to next-generation firewalls, there is a wide array of tools available to enhance the security of remote work environments.
One of the key technologies utilized in securing remote work is Virtual Private Networks (VPNs). VPNs establish secure and encrypted connections between remote employee and their organization’s network, ensuring that data transmitted over public networks remains private and protected.
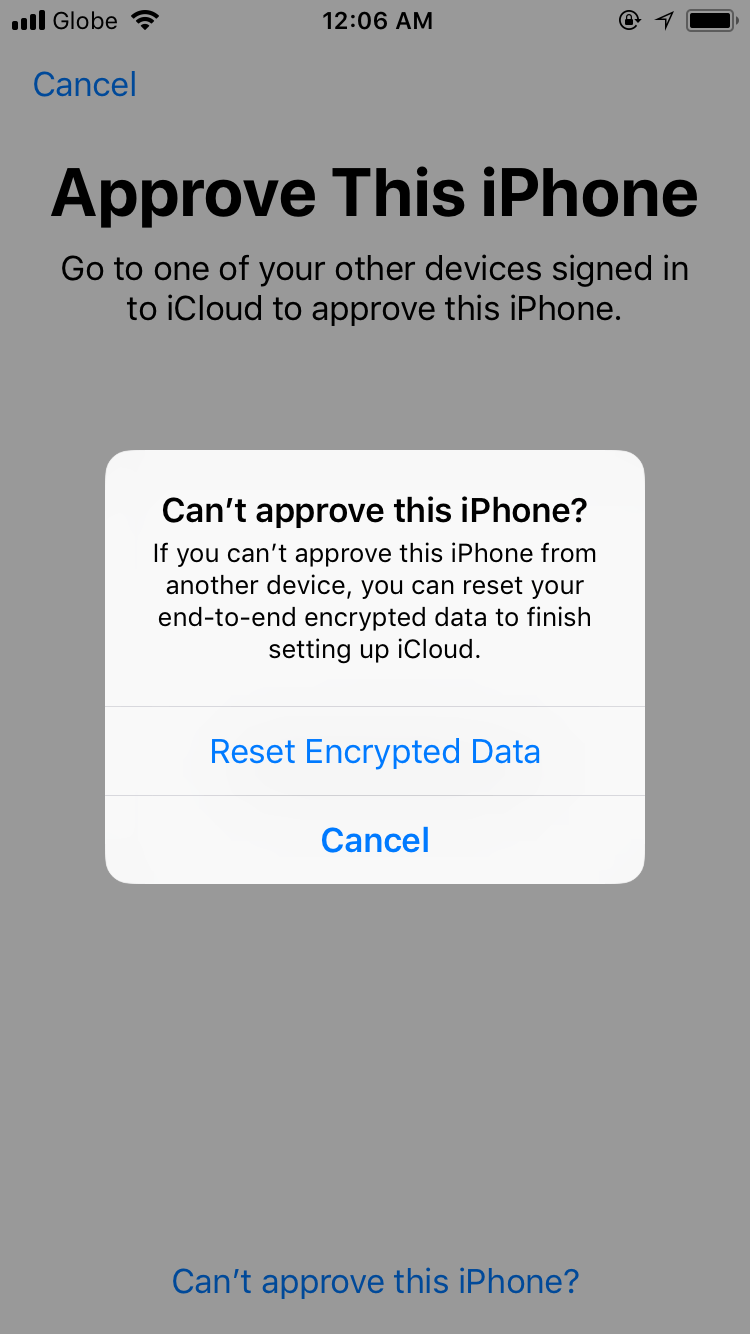
Furthermore, multi-factor authentication (MFA) is becoming increasingly prevalent in remote work settings. By requiring users to provide two or more pieces of evidence to verify their identity, such as a password and a unique code sent to their mobile device, MFA adds an extra layer of security, reducing the risk of unauthorized access.
Importance of Regular Security Audits and Updates
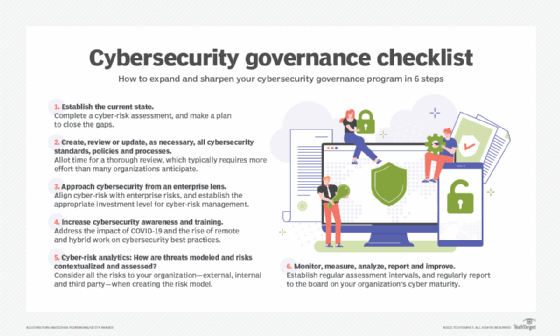
Even with robust security measures in place, organizations must conduct regular security audits and updates to identify vulnerabilities and address them promptly. This includes reviewing and updating software, patching security flaws, and analyzing the effectiveness of existing cybersecurity protocols.
Penetration testing, or ethical hacking, is another valuable practice that allows organizations to assess the effectiveness of their security defenses. By intentionally attempting to exploit vulnerabilities, organizations can identify weak points in their systems and enact appropriate countermeasures.
Additionally, staying informed about the latest cybersecurity threats and trends is paramount. Cybercriminals are constantly evolving their tactics, and organizations must keep up to date with the latest security practices to stay one step ahead.
Hybrid Model and Cybersecurity
As the world adapts to the new normal, the future of work may involve a hybrid model that combines in-person and remote work. This presents both challenges and opportunities for cybersecurity.
A hybrid model requires organizations to ensure that their security infrastructure can support a seamless transition between the office and remote work environments.
Moreover, as companies embrace flexibility and remote work options, they need to address potential cybersecurity gaps that may emerge when employees alternate between different locations and networks. This may involve implementing strict access controls, regularly monitoring employee devices, and securely managing data across various environments.
The key is to establish a comprehensive cybersecurity strategy that considers the unique requirements of both in-person and remote work scenarios, prioritizing the protection of sensitive data and maintaining a robust defense against cyber threats.
Beyond Remote Work
The challenges and solutions presented by cybersecurity in a work-from-home environment have broader implications for the future of cybersecurity as a whole. As technology evolves and our reliance on digital platforms increases, the need for robust cybersecurity measures becomes paramount.
Cybersecurity professionals will need to constantly adapt and develop innovative strategies to protect against emerging threats. Collaboration between public and private sectors, cybersecurity experts, and governments will be crucial in creating a secure digital ecosystem.
Ultimately, the question of whether cybersecurity can work from home should not be seen as a binary choice. Rather, it is an ongoing process that requires constant vigilance, education, and the integration of advanced technologies. By prioritizing cybersecurity in our remote work practices, we can create a safer and more resilient digital landscape for all.
Frequently Asked Questions
Here are some common questions regarding the feasibility of working from home in the field of cybersecurity.
1. How can cybersecurity professionals effectively work from home?
Working from home in cybersecurity requires a few essential measures to ensure effectiveness. First, professionals need a secure and stable internet connection to handle their day-to-day tasks. It’s also important to have access to a reliable VPN (Virtual Private Network) to protect sensitive data and securely connect to work resources.
Cybersecurity professionals should use encrypted communication tools and follow best practices for securing their home networks.
Moreover, setting up a dedicated workspace at home can contribute to productivity. This means having a separate area where professionals can focus, away from distractions. Regular communication and collaboration with team members and supervisors using secure channels are also crucial for successful remote work.
2. Can cybersecurity teams maintain the same level of security when working remotely?
Absolutely! While working remotely, cybersecurity teams can uphold the same level of security as they would in a traditional office setting. By implementing strong security measures, such as using multi-factor authentication for all accounts and employing robust encryption methods, teams can maintain a high level of security.
Additionally, maintaining strict security protocols, adhering to cybersecurity best practices, and conducting regular security audits are essential. Remote work should not compromise the adherence to policies and procedures that govern the protection of sensitive data.
By staying vigilant and consistently implementing security measures, cybersecurity professionals can ensure the same level of security while working remotely.
3. Are there any challenges associated with remote work in cybersecurity?
While remote work in cybersecurity offers numerous benefits, there can be a few challenges to overcome. One of the major challenges is the potential risk of cyber threats targeting home networks or unsecured devices. To mitigate this risk, professionals need to secure their home networks, use encrypted connections, and regularly update their devices with the latest security patches.
Another challenge is maintaining effective communication and collaboration among team members. Cybersecurity professionals need to ensure they have efficient communication channels and tools in place to exchange information, discuss security incidents, and provide support to one another. Regular virtual meetings and clear communication protocols can help overcome this challenge.
4. How does remote work impact incident response in the field of cybersecurity?
Remote work does not necessarily hinder incident response in cybersecurity. In fact, with the right tools and protocols in place, incident response can be efficiently managed, even when teams are working remotely. Establishing incident response plans and ensuring all team members are aware of their roles and responsibilities is crucial.
With remote access to necessary systems and resources, cybersecurity professionals can quickly identify and respond to security incidents. By utilizing remote incident response platforms, teams can effectively collaborate, investigate incidents, and take appropriate actions to mitigate risks and resolve issues promptly.
5. How can organizations support remote cybersecurity work?
Organizations can support remote cybersecurity work by providing the necessary resources and tools for employees to perform their tasks securely from home. This includes ensuring the availability of secure VPN connections, access to necessary systems and tools, and regular training on remote security practices.
Additionally, organizations should foster a culture of cybersecurity awareness and encourage employees to adhere to best practices in their remote work environments. Regular communication and collaboration platforms should be in place to facilitate seamless teamwork and knowledge sharing.
By investing in the right technology and prioritizing the well-being and productivity of their remote cybersecurity teams, organizations can support and enable successful remote work.
Let’s wrap things up! Cybersecurity is super important when working from home. It helps protect our personal information and keeps hackers away. Having a strong password, using antivirus software, and being careful with email attachments are some ways we can stay safe.
We should also update our devices regularly and avoid clicking on suspicious links. By following these tips, we can work from home securely and enjoy the benefits of technology without worries!
Remember, cybersecurity doesn’t have to be complicated. It’s just about taking some simple steps to stay safe online. So, whether we’re studying, gaming, or chatting with friends, let’s keep our virtual doors locked and our digital selves protected. Stay smart, stay safe!