Geo-fencing, huh? Ever heard of it? Well, let me tell you, it’s a pretty nifty concept! So, here’s the big question: Can Geo-fencing Prevent Unauthorized Access? Sounds intriguing, doesn’t it? Let’s dive right in and find out!
Imagine this: You’re wandering around with your smartphone, and suddenly, you come across an off-limits zone. But wait! Before you can even take a step inside, your phone buzzes with a warning. That’s the power of geofencing! It’s like having an invisible forcefield that keeps unwanted intruders at bay.
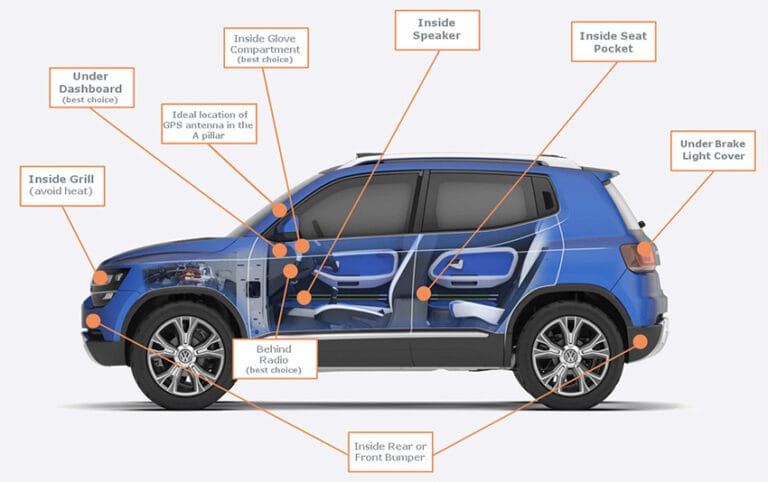
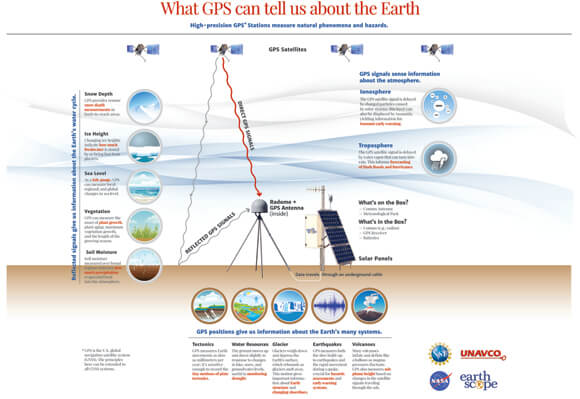
But how does it work? Well, my curious friend, geo-fencing uses the magic of GPS and good old technology to create a virtual boundary.
This boundary can be set up around a physical location, like your house or a restricted area. When you approach or cross this boundary, geofence sensors in your devices (like your phone) send signals, and voila! You’ll receive a notification, alerting you to back off unless you want trouble.
Now, let’s get back to our question: Can Geo-fencing Prevent Unauthorized Access? Stick around, and we’ll explore the ins and outs of this cutting-edge technology, and discover how it can keep unwanted guests at bay. Get ready for an adventure into the realm of geofencing!
Can Geo-fencing Prevent Unauthorized Access?
Geo-fencing is an effective tool for preventing unauthorized access. By setting up virtual boundaries, it enables businesses to control and monitor access to specific locations or assets.
Geo-fencing utilizes GPS or RFID technology to trigger alerts or actions when a device or person enters or exits a designated area.
This proactive approach improves security by providing real-time notifications and automating responses. With geo-fencing, organizations can enhance access control, protect sensitive areas, and prevent unauthorized entry.
Understanding Geo-fencing
Geo-fencing is a location-based technology that utilizes GPS, RFID, Wi-Fi, or cellular data to create virtual boundaries around a physical location or device.
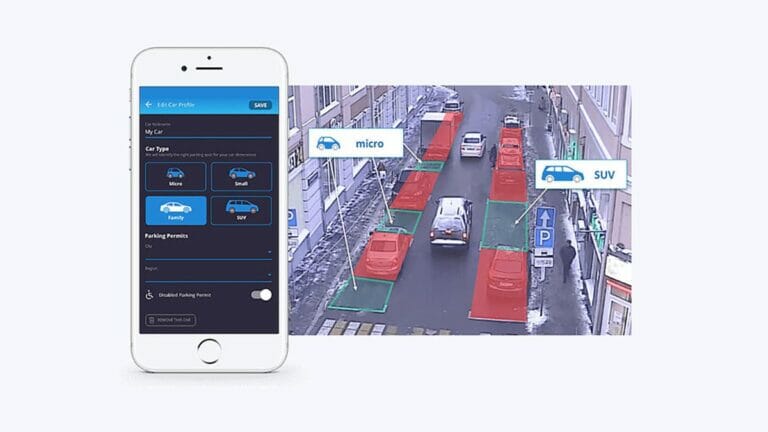
These virtual boundaries can be customized to suit specific needs, such as prohibiting access to sensitive areas or triggering notifications when someone leaves or enters a designated space.
Implementing geo-fencing involves defining the boundaries, setting up triggers, and establishing actions or notifications to be taken when those triggers are activated.
For example, a business may set up a geo-fence around its office and configure it to send an alert to the security team whenever an unauthorized person enters the premises.
The technology can be applied to various scenarios, including smart homes, schools, businesses, and even government institutions.
One common application of geo-fencing is in mobile devices. Companies can use geo-fencing to restrict access to certain features or content based on the user’s location.
For instance, a parent may set up a geo-fence around their child’s school, preventing them from using certain apps or accessing the internet during school hours.
Benefits of Geo-fencing
Geo-fencing offers several benefits when it comes to preventing unauthorized access. Let’s explore some of these advantages:
- Enhanced Security: By setting up geo-fences around sensitive areas or devices, organizations can significantly bolster their security measures. Unauthorized access attempts can be immediately identified, allowing for prompt action to be taken.
- Efficient Monitoring: Geo-fencing provides real-time monitoring capabilities. With appropriate triggers and notifications in place, security personnel can stay informed about any unauthorized access attempts, ensuring a rapid response.
- Customizable Boundaries: Geo-fences can be easily defined and customized to suit specific needs. This flexibility allows organizations to adapt their security measures based on the unique requirements of the environment.
Limitations of Geo-fencing
While geo-fencing offers several benefits, it is important to understand its limitations. Here are a few factors to consider:
- Technical Complexity: Implementing and managing a geo-fencing system can be technically challenging, particularly for organizations with limited resources or expertise. It requires the integration of various technologies and careful configuration to ensure optimal functionality.
- Location Accuracy: Geo-fencing relies on location data, which may not always be 100% accurate. Factors such as GPS signal strength and environmental obstructions can affect the precision of the virtual boundaries. This can lead to false positives or negatives, potentially compromising security measures.
- Privacy Concerns: The use of geo-fencing involves the collection and processing of location data, which raises privacy concerns. Organizations must handle this data carefully and ensure compliance with relevant regulations to protect the privacy rights of individuals.
Tips for Effective Geo-fencing
To maximize the effectiveness of geo-fencing in preventing unauthorized access, consider the following tips:
- Define Clear Boundaries: Take the time to accurately define the boundaries of your geo-fence, ensuring they align with your security needs and objectives.
- Establish Appropriate Triggers: Identify the events or actions that should activate a notification or action. This could be someone breaching the geo-fence or a specific period.
- Regularly Test and Update: Geo-fencing systems require regular testing and updating to ensure they are functioning as intended. This includes verifying the accuracy of the virtual boundaries and evaluating the triggers and notifications.
Geo-fencing is a powerful tool that can contribute to preventing unauthorized access in various settings. However, it is vital to recognize both the benefits and limitations of this technology.
By understanding its capabilities and implementing best practices, organizations can harness the potential of geo-fencing to enhance their security measures and protect against unauthorized access.
Frequently Asked Questions
In this section, we will address some common questions about geo-fencing and its role in preventing unauthorized access.
How does geo-fencing work?
Geo-fencing uses GPS, Wi-Fi, or cellular data to create a virtual boundary or perimeter around a physical location. When a device enters or exits this boundary, it triggers predetermined actions or alerts. Geo-fencing can be applied to various devices, such as smartphones, tablets, or vehicles, to track their movements and monitor locations.
For example, a business can set up a geo-fence around its premises, and when a device enters this area, it can send a notification to the owner or security personnel. This technology enables businesses to have better control over access to certain areas and improve security measures.
Can geo-fencing prevent unauthorized access?
While geo-fencing alone cannot completely prevent unauthorized access, it can be an effective tool in deterring and detecting such instances.
By setting up geofences at key entry points and sensitive areas, businesses can receive immediate alerts when someone attempts to breach these boundaries.
In addition to real-time notifications, geo-fencing can also provide valuable data for analysis and investigations. It allows security teams to identify patterns, track movements, and gain insights into potential vulnerabilities. By acting upon this information, businesses can take proactive measures to prevent unauthorized access and enhance their overall security measures.
What are the benefits of using geo-fencing for security purposes?
One of the significant benefits of using geo-fencing for security purposes is the ability to create custom boundaries and tailor security measures accordingly.
Businesses can define specific areas where unauthorized access is a concern and receive alerts whenever someone enters or exits these zones.
Furthermore, geo-fencing allows for the integration of other security technologies, such as surveillance cameras or access control systems. When an unauthorized individual is detected within a geo-fenced area, the system can trigger actions like activating alarms or locking doors, providing an immediate response to potential security threats.
Does geo-fencing work in real-time?
Yes, geo-fencing works in real-time. As soon as a device breaches the defined virtual boundary, the system immediately registers and sends out the necessary alerts or actions.
This real-time functionality is crucial for businesses to respond promptly to security breaches and potential threats.
However, it is important to note that the effectiveness of real-time geofencing relies on factors such as the accuracy of GPS or Wi-Fi signals and the responsiveness of the monitoring system. Regular checks and testing are necessary to ensure the system is functioning optimally.
Are there any limitations to using geo-fencing to prevent unauthorized access?
While geofencing has its advantages, there are some limitations to consider. One limitation is the reliance on device-based tracking. If someone gains unauthorized access without carrying a tracked device, they can bypass the geo-fencing system.
Additionally, factors such as GPS signal accuracy, device battery life, and potential interference can impact the effectiveness of geo-fencing. It’s important for businesses to regularly assess and update their geo-fencing systems to address these limitations and ensure optimal performance.
Geo-fencing is a technology that can help prevent unauthorized access to certain areas. It uses GPS or RFID signals to create virtual boundaries and send alerts when someone enters or exits those boundaries.
This can be useful in various situations, such as protecting personal data, securing physical locations, or ensuring the safety of children. However, there are limitations to geo-fencing, as it relies on the accuracy of GPS signals and can be affected by signal interference and battery life.
Privacy concerns arise when this technology is used to track individuals’ movements. While geo-fencing can be an effective tool in certain scenarios, it is important to consider the potential drawbacks and ensure that it is used responsibly.